-
Cyber Attacks – What defences do you have?

The best strategy for combating cyber attacks, is to adopt automation and 24/7 monitoring. In addition to the comprehensive monitoring capabilities of our software, we employ several other defences to protect against cyber threats. One crucial aspect of our strategy is the adoption of advanced automation techniques. We can swiftly respond to threats and minimise…
-
Why You Need a PC Clean

A PC clean is an part of your IT policies if you want your equipment to be reliable. Spring Cleaning Lots of people give their homes a good spring clean, getting rid of dust that has built up and helping everyone breathe easier, and this also works for computers. Dust in your house (and computer)…
-
Incident Response – Talk about bad timing!
In response to Clive’s Blog on Smart Thinking about incident response – he couldn’t have picked a worse time. Right in the middle of putting together and planning some of the largest projects we have in the pipeline and organising the day-to-day support work – I did not want to play! (Clive said he wouldn’t…
-
IT Monitoring – Who Watches What?

I thought I would let you all know about some of the tools we use for IT monitoring to keep an eye on your systems. Below are a couple of technologies that we recommend to our clients. They just give you that extra peace of mind to know that we can monitor what is going…
-
Will Robots Rule the World?

Robots? Clive did not know for sure but he gave a good answer… A couple of weeks ago we were invited to speak to a Zoom meeting and this was basically a Question and Answer session. After reassuring the group that no question was too silly to ask, just that nobody had been brave enough…
-
Go Pro or go Home?
One of our larger clients recently approached us to find them an additional laptop for one of their staff with some specific requirements. They wanted it to be light, have a small form factor at 13” or less, be reasonably powerful and also be cheap at around £600. They also requested that it not be…
-
Linux for Business (Part I)

Most of us use a computer running Microsoft Windows for work – I do – some of us use an Apple Mac or a Chromebook and an even smaller number use a computer not running one of those mainstream operating systems – Linux. Linux has a major advantage when it comes to using it in…
-
BMW Head Unit Update

I’ve had the itch for a sportier car for a while and after some looking around and research on model in my price range; I settled for a BMW M135i, something modern enough for my technology centric personality, but simple enough for me to get my hands dirty maintaining and modifying it. BMW’s are easy…
-
So your Mum is a geek!

I have regularly written geek present lists for Christmas and Father’s Day, but I have been amiss when it comes to Mother’s Day – the last one was back in 2019: Embed A Geek Mother’s Day – Ten presents for the Geek in your Mum – Octagon Technology That is going to be fixed now…
-
A patch in time!
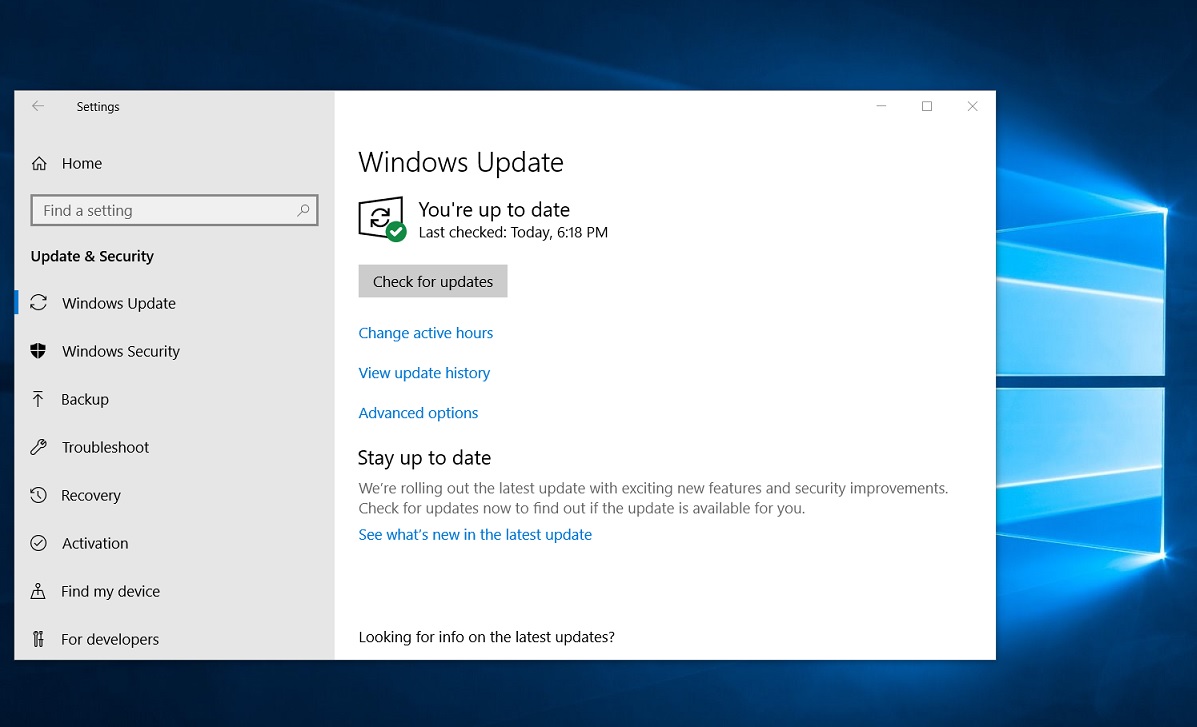
A client recently brought their laptop to us as they were unable to get remote support. They had very likely been the victim of a scam which had cost them a significant sum of money. They wanted us to check their computer for malware and see the offending emails. This proved tricky as none of…
-
Ransomware: Is it a Threat? – Part 1

Ransomware is still a threat to you Without a doubt ransomware is one of the most serious cyber security issues an organisation faces (UK Government. 2022). Here is a recent story from the tech press, showing how organised and determined the gangs that operate these types of cyber attack are. The Unrelenting Menace of the…
-
The rise and fall of removable media

As many may remember, early computers were fairly useless by themselves. Personal computers such as the C64, Amiga, Atari and Spectrum did not have any internal storage, some did not even have a drive to accept a disk or tape and required peripherals to load data. As such people frequently found themselves with multiple boxes…

